Vpn access abstract concept vector illustration. virtual private network access, remote proxy server, vpn service, unblock | CanStock

Virtual private network Private Internet Access Proxy server NordVPN, Special, winter, logo, computer Wallpaper png | PNGWing

VPN Access Abstract Concept Vector Illustration. Stock Vector - Illustration of isolated, computer: 194531662

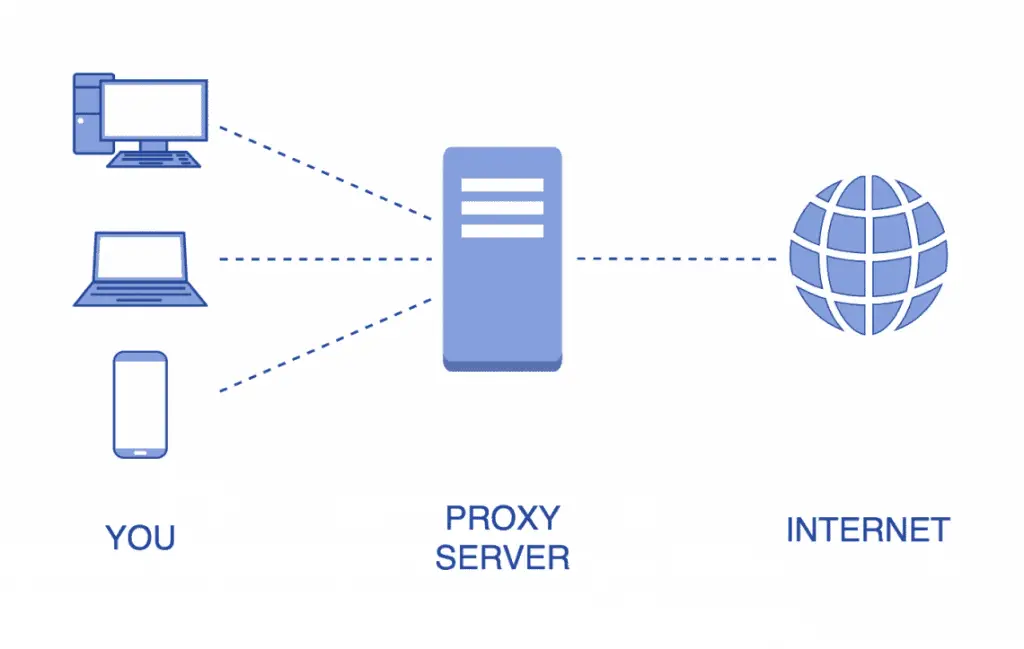
How to use AWS PrivateLink to secure and scale web filtering using explicit proxy | Networking & Content Delivery
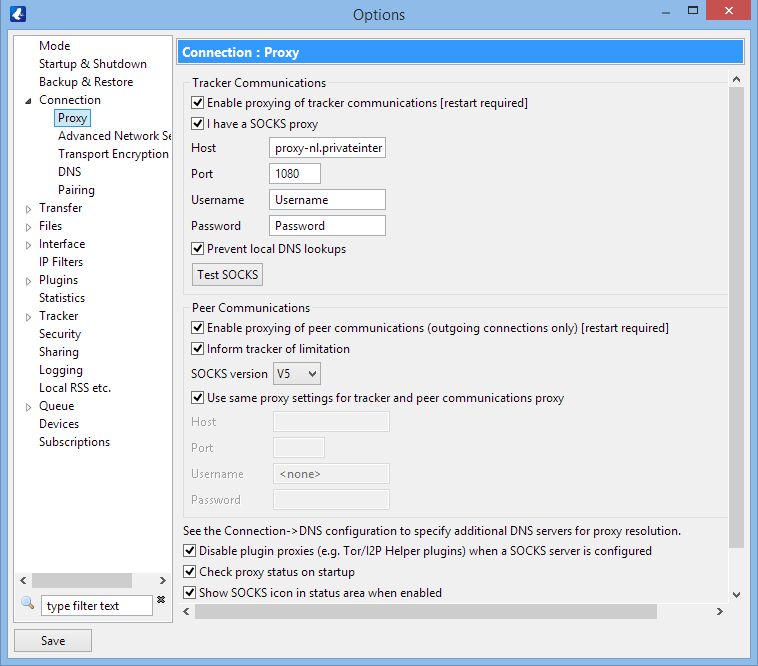
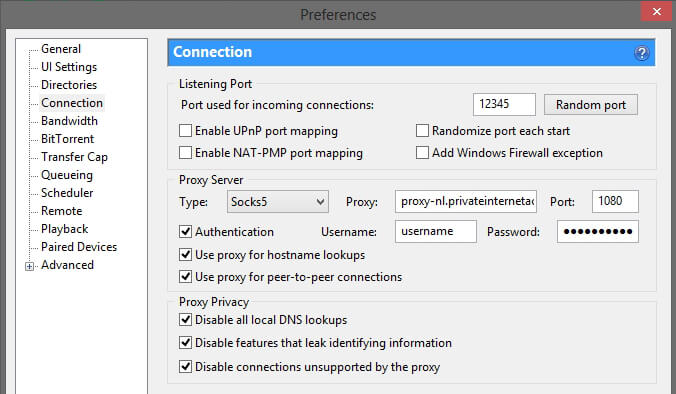
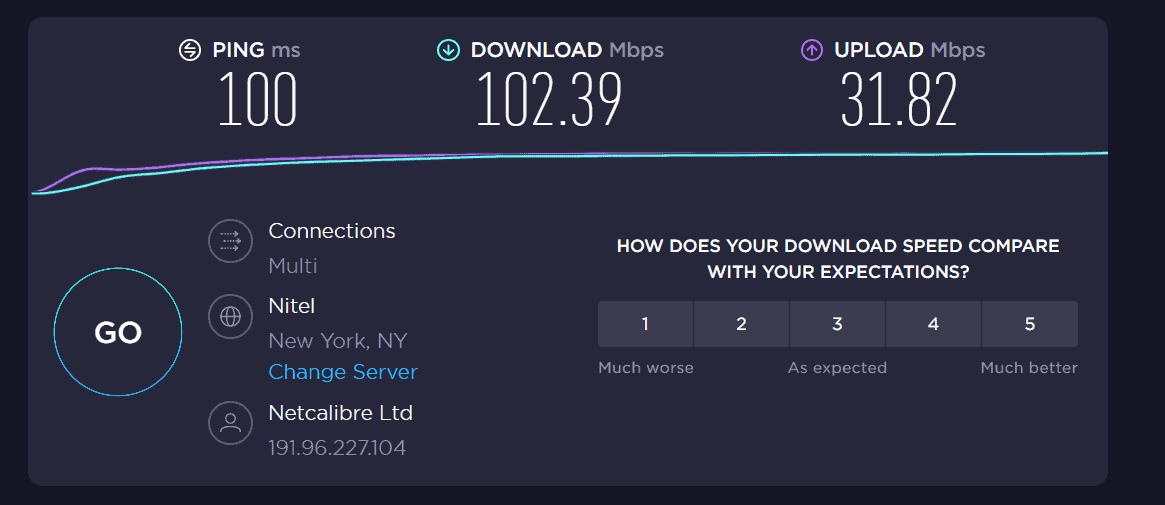
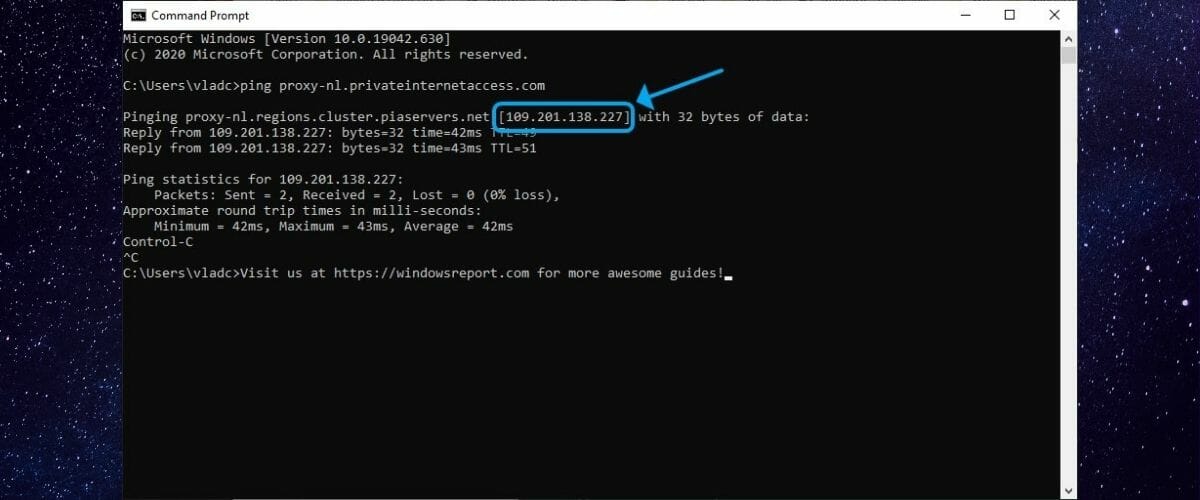
Torrenter og privat internetadgang (Den ultimative guide til at bruge PIA som en torrent VPN eller proxy)
Virtual private network Computer security Computer network Point-to-Point Tunneling Protocol Encryption, vpn transparent background PNG clipart | HiClipart
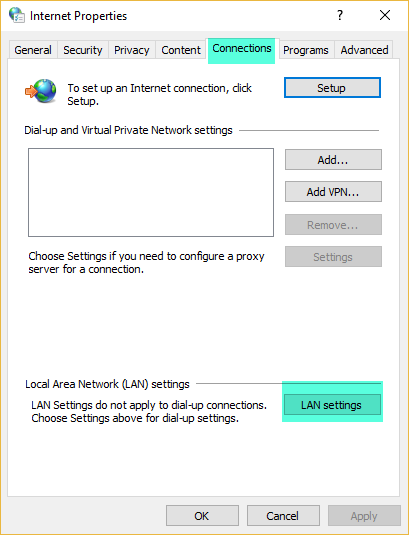
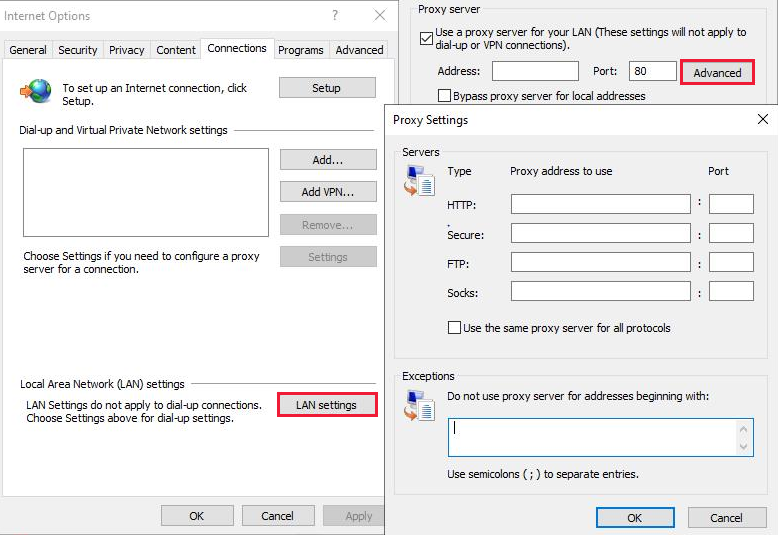
How to bypass a Proxy Server using the Application .config file for a Vault client or integration | Vault Products | Autodesk Knowledge Network



![Private Internet Access (PIA) Review [2022]: Is It a Good VPN? Private Internet Access (PIA) Review [2022]: Is It a Good VPN?](https://www.safetydetectives.com/wp-content/uploads/2021/12/PIA-review-4.png)